[Post 25 – 30 in 30]

Cybersecurity is no longer a luxury but a necessity. However, as the recession looms, budgets are becoming tighter, leading companies to rethink their cybersecurity investments. How, then, should businesses optimize their limited budgets to ensure robust cybersecurity? Let’s break it down.
A Bird’s Eye View of Cybersecurity Threat Landscape
Recent research indicates that large organizations use nearly 100 different security tools. Yet, even with such a vast arsenal, cyber-attacks continue to infiltrate these businesses, as evidenced by the recent Gateway Casino cyber attack.
To make matters worse, it’s predicted that budgets will continue to be strained due to a possible recession in 2023. This makes it even more crucial for companies to smartly allocate their cybersecurity investments.
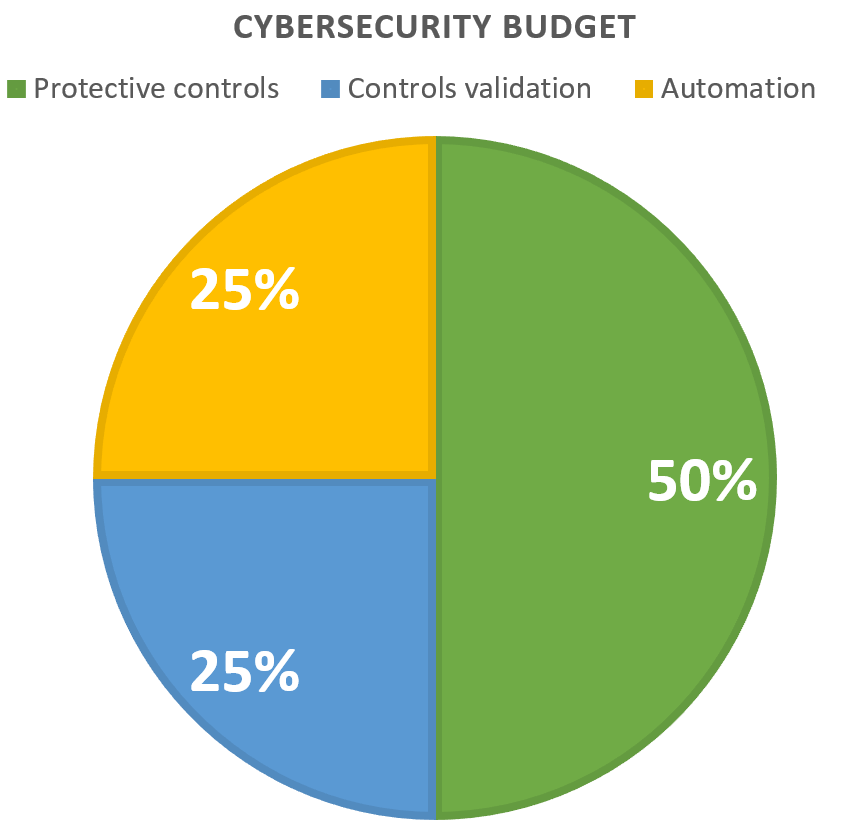
So, where do we begin? Let’s look at the three key areas where your cybersecurity budget should be focused: protective controls, controls validation, and automation.
1. Protective Controls
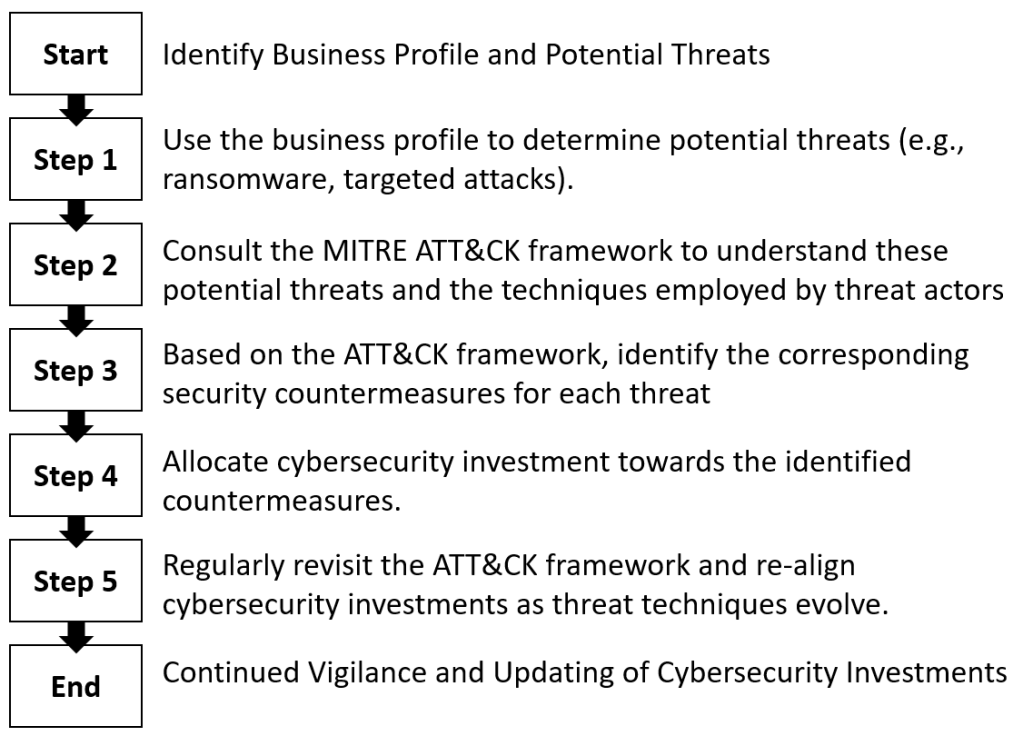
Just like doctors use patient profiles to prioritize treatments, we can use business profiles to understand and prepare for potential cyber threats. For instance, while ransomware is a risk for all businesses, some companies, like technology providers, face the additional threat of being exploited to access customer environments.
To simplify, protective controls are the measures you take to guard against threats. Think of it like putting a lock on your front door or installing a security alarm at your office – you’re implementing measures that make it harder for bad actors to gain access.
An excellent resource for understanding the techniques used by threat actors and appropriate countermeasures is the MITRE Corporation’s ATT&CK framework. It’s a comprehensive, free-to-use guide that helps you familiarize yourself with various threats and corresponding security countermeasures.
2. Controls Validation
While implementing protective controls is crucial, it’s equally important to regularly test these controls to ensure they’re working as intended. This process, known as controls validation, is much like a fire drill – you’re testing your preparedness for a possible cyber attack.
A few common ways to do this include:
- Penetration testing or Red Teaming, where you simulate a cyber attack to see how your defenses hold up.
- Purple Teaming, where the two teams collaborate openly. The Red Team shares its attacking methods, while the Blue Team explains their defensive strategies. This way, both teams learn from each other, strengthening the organization’s overall security posture. It’s like a friendly scrimmage where both teams are on the same side: protecting the organization.
- Compliance audits with Independent third-party auditors evaluate if your controls comply with standards such as ISO 27001 or NIST and if they are maintained and improved.
- Self-Assessments: Internal evaluation of your controls using checklists or frameworks like NIST’s Cybersecurity Framework to review their effectiveness.
3. Automation
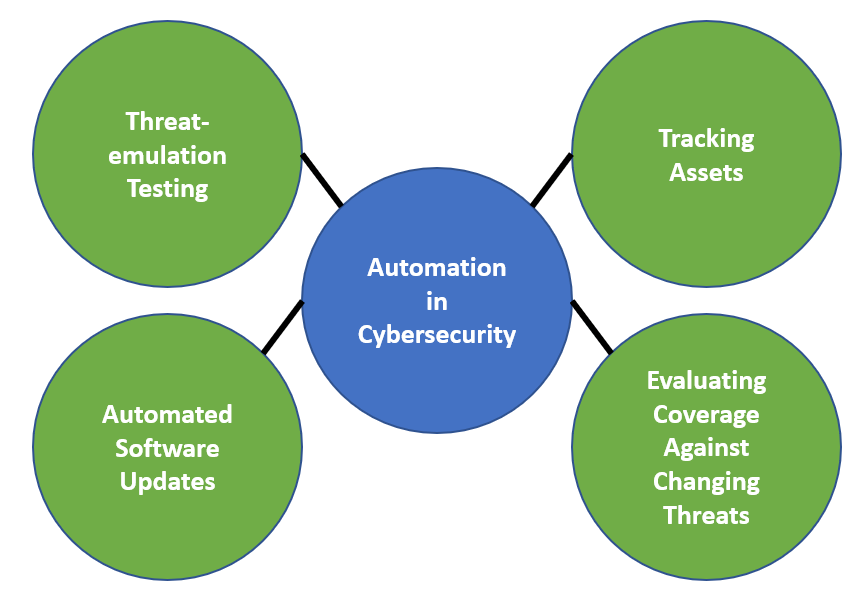
With the complexity and scale of technology environments growing rapidly, manually managing your security posture is becoming impractical. Automation of cybersecurity processes not only increases efficiency but also reduces the likelihood of human error, a significant cause of security breaches.
Consider using Security Orchestration and Automated Response (SOAR) tools and automated software updates wherever possible. Automation can also assist in tracking the security status of your assets, evaluating coverage against changing threats, and simulating threat scenarios.
In addition to automation, integrating Managed Detection and Response (MDR) services into your cybersecurity strategy can significantly improve threat detection, response time, and overall security resilience.
Here are some of the core components of MDR services:
- Advanced Threat Detection: MDR providers use sophisticated tools and techniques such as Endpoint Detection and Response (EDR) technology, behavior analytics, and machine learning to detect advanced threats that traditional security measures may miss. They continually monitor network activity to identify anomalies and potential threats.
- Threat Intelligence: MDR providers also leverage threat intelligence – up-to-date information about emerging threats and attack strategies – to help organizations stay ahead of potential attacks. They use this information to improve detection capabilities and devise effective response strategies.
- Incident Response: When a threat is detected, MDR providers quickly step in to respond. They help to contain the threat, mitigate the damage, and eliminate the source of the attack. The goal is to reduce the time it takes to respond to an attack (response time), thereby minimizing potential harm.
- 24/7 Monitoring: Cyber threats can happen at any time, and waiting until the next business day to respond can result in significant damage. MDR providers offer around-the-clock monitoring to ensure immediate response to any security incidents.
- Expertise and Consultation: MDR services are not just about technology; they also bring cybersecurity expertise to the table. They provide advice and guidance on improving security posture, understanding threat landscapes, and complying with industry regulations.
- Remediation Guidance and Support: Post-incident, MDR providers offer remediation support to ensure that vulnerabilities are patched, systems are secured, and the chances of a similar breach in the future are minimized.
Overall, MDR services offer proactive and continuous security monitoring, detection, and response activities that can enhance an organization’s cybersecurity capabilities, especially if internal resources are limited.
Takeaways
With a constrained budget, focusing your cybersecurity investment becomes even more critical. Using authoritative security frameworks, understanding the nature of potential threats, utilizing automation and 3rd party MDR services when possible, can significantly improve your security posture. Your cybersecurity strategy should be adaptive and resilient, ready to respond to the ever-changing threat landscape.
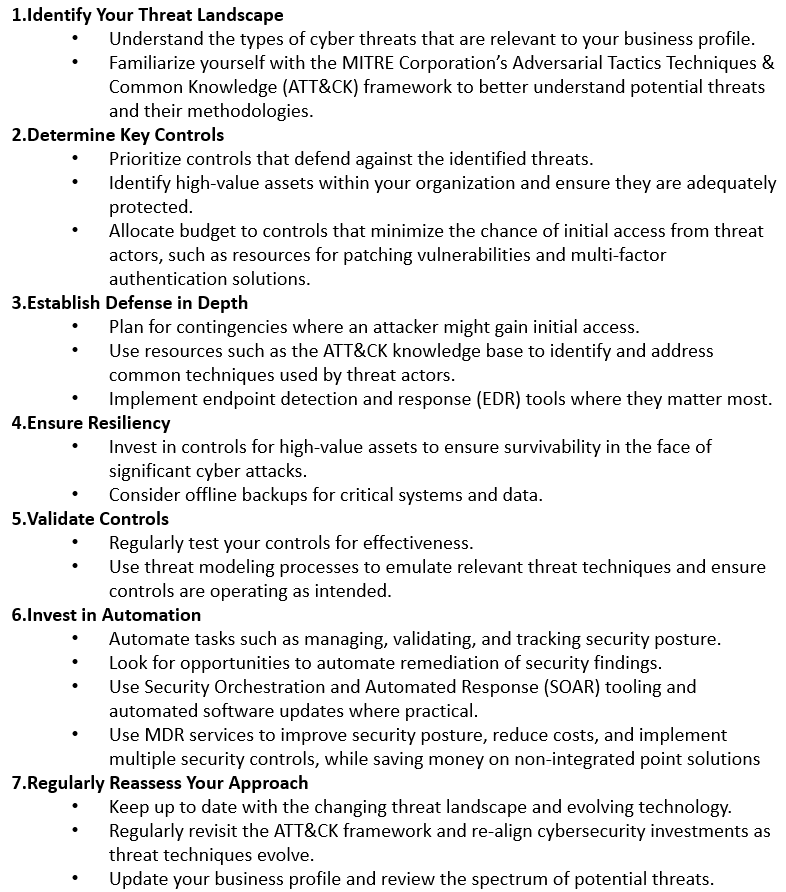
Remember, cybersecurity is not a one-size-fits-all solution. As your business profile, technological complexity, and threat landscape evolve, so should your cybersecurity strategy.
Don’t let a constrained budget discourage you. Even the most limited investments can significantly improve your cybersecurity posture if applied strategically. With focused investments, businesses can better protect their assets, reputation, and future.
Thanks for reading this far.
My aim with this campaign is to provide readers with valuable content, insights, and inspiration that can help in their personal and professional lives. Whether you’re looking to improve your productivity, enhance your creative strategies, or simply stay up-to-date with the latest news and ideas in cybersecurity, I’ve got something for you.
But this campaign isn’t just about sharing our knowledge and expertise with you. It’s also about building a community of like-minded IT and security focused individuals who are passionate about learning, growing, and collaborating. By subscribing to the blog and reading every day, you’ll have the opportunity to engage with other readers, share your own insights and experiences, and connect with people in the industry.
So why should you read every day and subscribe? Well, for starters, you’ll be getting access to some great content that you won’t find anywhere else. From practical tips and strategies to thought-provoking insights and analysis, the blog has something for everyone that wants to get current and topical cybersecurity information. Plus, by subscribing, you’ll never miss a post, so you can stay on top of the latest trends and ideas in the field.
But perhaps the biggest reason to join the 30-in-30 campaign is that it’s a chance to be part of something bigger than yourself. By engaging with the community, sharing your thoughts and ideas, and learning from others, you’ll be able to grow both personally and professionally. So what are you waiting for? Subscribe, and for the next 30 days and beyond, let’s learn, grow, and achieve our goals together!
Discover more from Designing Risk in IT Infrastructure
Subscribe to get the latest posts sent to your email.
One thought on “Where to Focus Your Company’s Limited Cybersecurity Budget: A Simplified Guide”
Comments are closed.