
Ransomware attacks have become increasingly common in recent years, and their impact can be devastating to businesses of all sizes. On April 16th 2023, Canadian company Gateway Casinos was hit by a ransomware attack that forced them to shut down their operations temporarily.
(As of the publishing date of this article April 25th 2023, the Casinos are still down)
April 21, 2023 – Gateway Casinos and Entertainment locations in Ontario will remain closed through the coming weekend as we continue to work on resolving a cybersecurity incident and put in place the plans for reopening at each location.
The attack resulted in significant, but yet to be quantified financial losses for the company. It is not yet known if they had to pay a ransom to the attackers to regain control of their systems.
In this blog post, we will discuss the various costs associated with a ransomware attack, and how they may affect Gateway Casinos.
1. IT Remediation Costs:

The first and most obvious cost associated with a ransomware attack is the cost of remediation. This includes the cost of identifying and fixing the vulnerability that allowed the attack to occur, as well as the cost of restoring systems and data that were affected by the attack. In the case of Gateway Casinos, the company had to hire a team of IT experts to assess the damage caused by the attack and restore their systems, which will result in significant expenses. This type of service is called IR, or Incident Response.
Here is a step-by-step process for incident response in a ransomware attack:
- Detection: The first step is to detect the ransomware attack. This can be done through various methods, such as system alerts, abnormal network traffic, or user reports.
- Containment: Once the attack has been detected, the next step is to contain the ransomware to prevent it from spreading further. This may involve disconnecting infected systems from the network or shutting down affected systems.
- Investigation: Once the ransomware has been contained, it’s time to investigate the attack. This involves analyzing the systems and network logs to determine how the attack occurred and what systems and data have been impacted.
- Analysis: After the investigation, the next step is to analyze the ransomware to determine its type, behavior, and potential impact on the organization. This information can help in developing a response plan.
- Response: With a clear understanding of the ransomware and its impact, the organization can develop a response plan. This may involve restoring data from backups, negotiating with the attackers for the decryption key, or rebuilding systems from scratch.
- Recovery: Once the response plan has been executed, the next step is to recover the affected systems and data. This may involve restoring data from backups or rebuilding systems from scratch.
- Lessons learned: Finally, it’s important to conduct a post-incident review to identify any areas of weakness in the organization’s security posture and improve future incident response efforts.
Incident response in a ransomware attack requires a well-coordinated and timely response to limit the impact of the attack on the organization. IR organizations are very different than professional services or consulting organizations, that may have people with similar skill sets. The operational workflow, criticality in response and appreciation for client impact due to downtime, are much more focused with IR teams. Incident response can be engaged in a few different ways:
a) Proactively: An IR retainer is paid for by the client before an incident. This involves an environment assessment, asset documentation, and a detailed documented IR plan, with contacts, escalations and timelines. Some retainers also require a pre-paid block of hours that expire in a year. This requires the retainer to be re-purchased every year. Costs can be $10K-$20K on average. The benefit of a retainer are; faster time to active engagement, faster time to resolution, reduced hourly rates. Cyber insurance providers will often assign an IR organization to a policy, that they work with on a regular basis. IR retainers are commonplace when getting cyber insurance.
The average hourly cost for an incident response team can vary widely depending on several factors, including the level of expertise required, the severity of the incident, and the location of the team. Here are some rough estimates based on industry research and surveys:
Internal Incident Response Team: For a mid-level internal incident response team, the average hourly rate can range from $150-$250 per hour. However, for a more experienced and specialized team, the hourly rate can go up beyond that.
Third-Party Incident Response Team: Third-party incident response teams can be more expensive than internal teams due to their higher level of expertise and the need to compensate them for their travel and accommodation expenses. The hourly rates for these teams can range from $250-$450 per hour.
b) Retro-actively: The client does not have an IR retainer, but contacts an IR organization directly during the breach. This would be similar to trying to get seating fort a large group of people immediately at a high-end restaurant with no reservations. The client will have to make a flurry of phone calls, negotiations, gather quotes, compare and analyze IR company reputation and viability. Then they will need to make the executive decisions to move forward with a paid scoping exercise. This additional scoping cost would be several thousand dollars. The client would then get non-optimal hourly rates for the duration of the incident.
If we make some assumptions we can calculate the cost of this thus far:
- Assumption 1 – No dedicated internal IR team yet (being built). IT Ops with security SMEs only.
- Assumption 2 – Cyber Insurance leveraged for engaging IR team. (Costs will be calculated for IR, but some costs may not be covered.)
- Assumption 3 – Full time staff will be paid as per normal during the incident. Part-time staff will not be.
- Assumption 4 – IR team will work 24/7 until resolution.
- Assumption 5 – Annual retainer paid $18K
- Assumption 6 – IR rate $350 / hr
$350 *24*7 = $58,800 per week
2. Loss of Productivity:

When a company’s systems are down due to a ransomware attack, its employees cannot perform their duties, resulting in a loss of productivity. The longer it takes to restore the systems, the more significant the loss of productivity. Gateway Casinos had to close its casinos temporarily, resulting in a significant loss of revenue.
Here is a simple formula showing how much a breach causing complete IT services outage may cost, based on employee payroll.
(((U*hup)*1.3)*DT) = cost in productivity loss
where:
U = the number of infected users
hup = average hourly user’s pay
1.3 = overhead rate (use your organization’s rate)
DT = hours of downtime
The formula is constructed as follows. U is the number of infected users, times the hourly user pay (hup), multiplied by 1.3 (this overhead rate is flexible and represents the cost of indirect costs and benefits on top of hourly wages), which is then multiplied by downtime (DT) in hours. This portion of the formula calculates costs for the non-productive time spent by the user community.
- Assumption 7 – 100 concurrent full-time staff per location, averaging across Ontario locations
- Assumption 8 – 14 locations in Ontario are all down to the same degree.
- Assumption 9 – The averaged hourly wage for full-time employees is $45CAD / hr
- Assumption 10 – DT for users is capped at 8hrs per day
- Assumption 11 – All days of the week are taken into the calculation (SMTWTFS)
U=1400 (100 * 14 locations)
hup=45
DT= 56 per week (8hrs * 7 days)
(((1400*45)*1.3)*56) = $4,586,400.00 in weekly productivity loss
Internal IT Ops and Security SMEs may also be working overtime during this incident, which is another possible cost.
3. Reputation Damage:
A ransomware attack can have a severe impact on a company’s reputation. Customers may lose trust in the company’s ability to protect their data and may choose to take their business elsewhere. In the case of Gateway Casinos, the company’s reputation was affected, and it had to spend additional resources to rebuild its brand image.
This is hard to quantify. The leakage of customer data can result in a loss of confidence in an organization that took years to establish. In some cases, this trust cannot be fully regained, leading to the loss of existing customers and a difficulty in acquiring new ones. Additionally, a company’s brand and reputation can be compromised after a cyberattack, leading to consumer distrust and a perception of the organization as an unsafe option. Rebuilding this rapport can be a challenging and costly endeavor for the company in the long term.
Assumption 12 – Regaining customer trust is a multi-year process with considerable investment in marketing required.
I am putting a finger in the air and saying this may cost upwards of $1M per year.
4. Regulatory Fines:
Companies that are subject to data protection laws may face fines and penalties for failing to protect customer data adequately. In the case of Gateway Casinos, they may have faced regulatory fines if it was found that they did not have adequate measures in place to protect their customers’ data.
I am not a lawyer, nor do I play one on TV or the internet, so I do not know what exposure Gateway has for regulatory fines. There may be some exposure to PIPEDA if it is found that personal information has been inadequately protected and leaked.
From PIPEDA section 28A
Offence and punishment
28 Every organization that knowingly contravenes subsection 8(8), section 10.1 or subsection 10.3(1) or 27.1(1) or that obstructs the Commissioner or the Commissioner’s delegate in the investigation of a complaint or in conducting an audit is guilty of
(a) an offence punishable on summary conviction and liable to a fine not exceeding $10,000
So for arguments sake, I’ll say $10,000 for fines.
5. Ransom Payment:
In some cases, companies may decide to pay the ransom demanded by the attackers to regain control of their systems. In the case of Gateway Casinos, it is still not determined if they chose to pay the ransom.
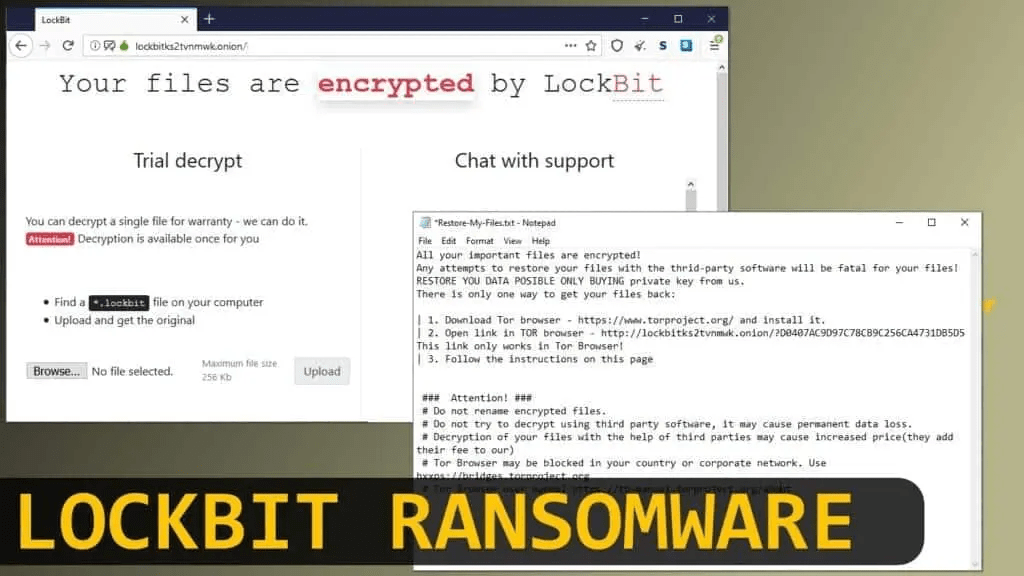
The ransom is usually calculated on a per-VM or per device/server/workstation basis. 1BTC is common. Using todays BTC market value which is $37,345.00, I will do the calculation.

Assumption 13 – 200 servers (all of which are virtual machines) have been encrypted
Assumption 14 – Local on-site backups have been compromised
Assumption 15 – Offsite backups will require approximately 1 week RTO (recovery time objective). Generally used for archival and not DR, or backup restoration.
The risk analysis has to be calculated to determine the best course of action.
Assumption 16 – Strategy B will be used to minimize downtime and minimize ransom.
a) Strategy A: Pay the ransom of $7,469,000 (200 x $37,345)
- Risk 1: Decryption key may not work
- Risk 2: Threat actor may use double extortion and ask for additional funds to not release personal information or company data
- Risk 3: There may be more than one threat actor in the environment. They could be attacked and ransomed continually by other actors if the environment is not forensically analyzed.
b) Strategy B: Negotiate with the ransomware group to get a flat rate, instead of per-VM. Lets say this is 50% of the original request, or $3,734,500.
- Risks 1-3 still apply
- Risk 4: Negotiation causes additional delay in restoration of services
c) Strategy C: Do not negotiate with ransomware group. Restore known-good backups in isolated environment. In parallel, continue with IR team to determine timeline, scope, root cause of breach, vector of attack, TTPs, isolation of internal threat, closing persistence channels / C2 , and plan to improve security posture.
- Risk 1: The time to recover may be considerable without local backups or a DR strategy.
- Risk 2: If backups have not been periodically tested, some servers may not be restorable and data loss is possible. If this is the case, then negotiating with ransom group would be the only option to restore data of those specific servers.
d) Strategy D: Go out of business and file for bankruptcy. Sell all assets to a third party and then rebuild the business from the ground up.
- Risk 1: This does not look good publicly. Its a career killer for all execs involved.
- Risk 2: It will take a long time to get back to black in this endeavor. Not for the faint of heart, and a lot of money will be lost.
6. Legal Costs:

The legal fees associated with a ransomware attack response can vary depending on various factors such as the severity of the attack, the complexity of the legal issues involved, the jurisdiction in which the attack occurred, and the legal services provider’s hourly rates.
Assumption 17 – The high end of the legal fees presented will be used for calculation.
In general, the legal fees associated with a ransomware attack response can include:
Legal consultation fees – These fees are charged by legal experts who provide initial advice and guidance on the legal aspects of a ransomware attack response, including potential liabilities, obligations, and risks.
These fees can range from $200 to $500 per hour, depending on the expertise and experience of the lawyers. Assuming a consultation lasts for two hours, the cost would be between $400 and $1,000.
Litigation fees – If the ransomware attack leads to litigation or legal disputes, legal fees for representation in court, discovery, depositions, and other legal proceedings may be incurred.
The cost of litigation fees can vary widely depending on the complexity of the case and the jurisdiction. Assuming a month-long engagement with two lawyers working on a medium complexity case, the cost can range from $50,000 to $100,000 or more.
Regulatory compliance fees – If the ransomware attack involves the compromise of sensitive or protected information, regulatory compliance fees may be incurred to ensure compliance with relevant data privacy and security laws.
Regulatory compliance fees will depend on the specific regulations applicable to the victim’s industry and the jurisdiction. Assuming a medium complexity case requiring compliance with several regulations, the cost can range from $10,000 to $50,000 or more.
Negotiation fees – If the victim decides to negotiate with the ransomware attacker, legal fees may be incurred for legal representation during negotiations.
The cost of negotiation fees can range from $200 to $500 per hour per lawyer. Assuming a negotiation lasts for 10 hours, the cost would be between $4,000 and $10,000.
Investigation fees – If the victim hires a legal firm to conduct an investigation of the attack, the legal fees for the investigation may be incurred.
The cost of investigation fees can vary widely depending on the scope and complexity of the investigation. Assuming a medium complexity investigation, the cost can range from $20,000 to $50,000 or more.
It is difficult to estimate the total legal fees associated with a ransomware attack response since they depend on various factors, and the cost can vary significantly from case to case. It is best to consult with a legal expert to determine the legal fees for a specific ransomware attack response.
I’m not a lawyer, but I will put a number up as a placeholder for this based on the above higher end range. $211,000
7. Lost Revenue:

It is difficult to estimate how much a single small casino makes in a day without specific information about the casino’s location, size, number of games offered, and other factors that can impact its revenue.
According to the American Gaming Association’s State of the States 2021 report, in 2019, the average daily gross gaming revenue (GGR) per commercial casino in the United States was approximately $409,000. However, this figure includes both small and large casinos, and the actual revenue for a single small casino can vary widely.
According to the Canadian Gaming Association’s 2019-2020 Annual Report, the Canadian gaming industry generated $17.1 billion in gross gaming revenue in 2019, with commercial casinos accounting for $8.6 billion of that total. This figure represents the entire Canadian gaming industry and includes both large and small casinos across the country.
Small casinos may make anywhere from a few thousand dollars to tens of thousands of dollars per day. The revenue will depend on various factors such as the size of the casino, the number of gaming tables and machines, the types of games offered, the location of the casino, and the overall economic conditions.
According to the same Canadian Gaming Association report, the average daily GGR per slot machine in Canada was $278 in 2019.
So for arguments sake I will only look at lost slot revenues, when in reality there is so much more to consider.
Assumption 18 – Only lost slot revenues are calculated.
Assumption 19 – The average number of slots across all 14 Gateway Casinos in Ontario is 400 per property
(14 sites * 400 * $278) = $1,556,800 lost revenue per day or $10,897,600 per week
It is important to note that the current pandemic has significantly impacted the casino industry’s revenue, and many small casinos have closed their doors permanently or temporarily. Therefore, any estimates should be approached with caution and based on the specific circumstances of the individual casino.
Total projected cost for 2 weeks of downtime at Gateway Casinos due to a ransomware attack:
IT Remediation Costs: $117,600
Loss of Productivity: $9,172,800
Reputation Damage: $1,000,000
Regulatory Fines: $10,000
Ransom Payment: $3,734,500
Legal Fees: $211,000
Lost Revenue: $21,795,200
Total: $36,041,100
In conclusion, a ransomware attack can result in significant costs for a company, both in terms of financial expenses and reputational damage. In the case of Gateway Casinos, the attack is resulting in significant financial losses and a damaged reputation, highlighting the importance of implementing robust security measures to protect against such attacks.
I must re-iterate, that these numbers are theoretical based on all the assumptions that I have listed in this article. I have taken many liberties in my assumptions and I do not represent that they are accurate in any way shape or form.
However, the logic is presented and the numbers will be updated as more information is available. Personally I think this number is very conservative, and the true number could be closer to $50M after all is said and done.
Collateral Damage:

It is one thing to have a single company lose tens of millions of dollars, but it is another to have a direct impact on the communities around it. These are the things that are also impacted because of the breach:
- Part-time workers that are not able to be scheduled, will not be paid for half a month. This will cause all kinds of hardship for hundreds, or thousands of people across the province. With the cost of living increasing, many people are living month-to-month, or paycheck-to-paycheck. Missing half a month of wages can have disastrously follow-on effects.
- Lost revenue to the cities and towns that rely on the casinos for a portion of their budget. This translates to higher taxes or fewer services for those living there.
- Possible site closures. If a site has to close to cut back expenditures, this further hits the community in jobs, revenue and tourism reduction. Thereby losing more potential revenue for other local small businesses.
Ransomware attacks can have a devastating impact on businesses, leading to data loss, financial damages, and reputational harm. To prevent ransomware attacks, companies should take a multi-faceted approach that includes both technical measures and employee training. Here are some steps that companies can take to prevent ransomware attacks:
- Keep software up-to-date: Regularly update software, including operating systems, antivirus software, and other security tools, to ensure they have the latest security patches and are protected against known vulnerabilities.
- Use strong passwords and multi-factor authentication: Ensure that all employees use strong, unique passwords and enable two-factor authentication for all accounts.
- Conduct regular backups: Regularly backup all important data, and store backups offline, so that they cannot be accessed by attackers. Regularly test backups to ensure that they can be restored in the event of a ransomware attack.
- Implement network segmentation: Segmenting the network can help prevent the spread of ransomware by limiting the attacker’s access to other parts of the network.
- Provide employee training: Educate employees on the risks of phishing emails and social engineering attacks, and provide regular training on how to identify and respond to potential threats.
- Threat detection and response: Use advanced threat detection tools to monitor networks, endpoints, and cloud environments in real-time for signs of suspicious activity. When a threat is detected, the company can respond quickly to contain and neutralize the threat before it can cause damage.
- Vulnerability management: Identify and prioritize vulnerabilities in your systems and networks, and develop strategies to address them before they can be exploited by attackers.
- Incident response planning: Develop and implement an incident response plan, including ransomware-specific response plans, to ensure a rapid and coordinated response in the event of an attack.
- Limit access to sensitive data: Restrict access to sensitive data to only those employees who need it to perform their job functions.
- Use encryption: Use encryption to protect sensitive data, both in transit and at rest.
- Continuous monitoring and testing: Provide continuous monitoring and testing of security systems and procedures to identify potential weaknesses and areas for improvement.
- Implement security best practices: Implement best practices for security, such as Zero Trust Architecture, least privilege access, centralized logging, etc.
- Use endpoint protection software: Consider using software that can detect and stop ransomware before it can encrypt files.
- Implement SASE / SSE: Use secure remote connectivity to access corporate resources and cloud services.
- Threat intelligence: Provide up-to-date threat intelligence to help your company stay informed about the latest ransomware threats and trends, and adapt your security practices accordingly.
These steps should be considered as a starting point, and each company should tailor their approach to ransomware prevention based on their unique risk profile and business needs.
Discover more from Designing Risk in IT Infrastructure
Subscribe to get the latest posts sent to your email.
One thought on “Calculating the cost of a breach – Casino Edition (Spoiler – over $36M)”
Comments are closed.