[Post 23 – 30 in 30]
Building an effective SOC is not a small task. It’s a considerable commitment of resources, time, and skill, but also a significant step towards ensuring your business’s cybersecurity.
This article will break down the key aspects of creating a SOC for small, medium, and large companies, addressing the estimated timeline, associated costs for staffing, and required software and hardware.
The Basics
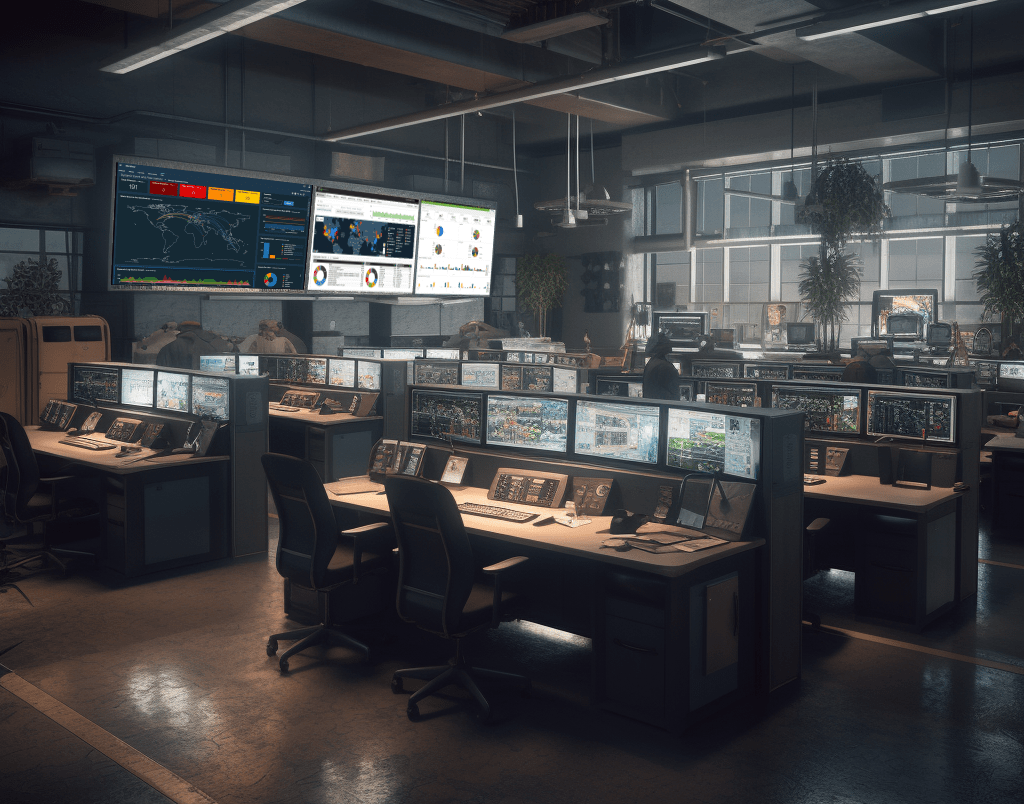
Before we dive into the details, it’s important to define what a SOC is. Simply put, a Security Operations Centre is a centralized unit that deals with security issues on an organizational and technical level. It houses a team responsible for monitoring and analyzing an organization’s security, ensuring appropriate defense measures are in place, and responding to any cyber threats.
Timeline for Building a SOC
The timeline for building a SOC depends on many factors, including the size of the company, available resources, the complexity of the existing network, and the company’s cybersecurity maturity level. However, a rough estimate could be:
- Small businesses: 6-12 months
- Medium businesses: 9-18 months
- Large businesses: 12-24 months
Remember, though, these are estimates and your timeline could vary depending on your specific needs.
Staffing Costs
Staffing a SOC is an ongoing expense that will make up a large portion of your operational costs. The staff size and structure will depend on the company’s size and the SOC’s scope. A small business may need a handful of security analysts, a manager, and perhaps a dedicated incident responder, whereas a large enterprise may require multiple teams covering different shifts, specializations, and regions.
The annual salary for a cybersecurity analyst in the Canada and United States averaged between $75,000 to $150,000, with managers and specialized roles commanding higher salaries. However, you should research current market rates in your region and industry.
The minimum number of people required to run a SOC effectively 24/7 will depend on several factors, including the size of the organization, its risk profile, the volume of security events, and the organization’s approach to shifts (e.g., 8-hour shifts vs. 12-hour shifts). However, let’s consider a medium-sized organization, using a typical 3-shift model for 24/7 coverage, and accounting for weekends and holidays.
1. Security Analysts:
This is the front line, monitoring alerts and alarms. Typically, you would need at least two analysts per shift to ensure that one person can take a break without leaving the SOC unattended. This means 6 analysts per day, and accounting for weekends and holidays, you’d need about 8-10 analysts in total for full coverage.
2. Incident Responders:
Depending on the volume of incidents, you may need 1-2 incident responders per shift, which translates to 3-6 per day. Including weekends and holidays, you’d need approximately 5-8 responders for full coverage.
3. Threat Hunters:
Threat hunting can often be a more flexible role and may not necessarily require 24/7 coverage. Instead, 1-2 threat hunters could work standard business hours, with additional time as required during active incidents.
4. SOC Manager:
Usually, you would have one SOC Manager who works standard business hours. However, they should be on call 24/7 in case of major incidents.
5. Security Engineers:
Similar to threat hunters, security engineers might not require 24/7 coverage. You might need 2-3 engineers working standard business hours, and possibly on a call rotation for off-hours emergencies.
6. Forensic Analysts:
Forensic Analysts are usually engaged as needed, rather than on a shift basis. You might have 1-2 forensic analysts who work standard business hours, but are available for serious incidents.
In total, this means you might need approximately 18-24 full-time-equivalent positions to run a medium-sized SOC effectively 24/7.
Keep in mind that this is a very rough estimate and actual staffing needs can vary widely depending on numerous factors. It’s also important to note that many SOCs make use of automation and orchestration tools to help manage the workload and reduce the need for human intervention in routine tasks.
Additionally, smaller organizations or those with fewer resources might opt for a shared SOC service or a managed security service provider (MSSP) to provide 24/7 coverage, rather than running their own SOC.
Software Costs
The software is the backbone of your SOC, used for detecting, analyzing, and responding to threats. This may include a Security Information and Event Management (SIEM) system, intrusion detection systems (IDS), intrusion prevention systems (IPS), endpoint protection platforms, threat intelligence platforms, and various other tools.
Costs can vary greatly depending on the chosen solutions and the size of your company. Some open-source options might work for small businesses, but larger enterprises will often require more robust and comprehensive (read: expensive) solutions. As a rough ballpark, software costs can range from $10,000 per year for a small company to several hundred thousand dollars for a large enterprise.
A SOC uses a variety of software tools to monitor, assess, and defend the information systems of an organization. Here are some of the commonly used types of software and examples of specific tools:
1. Security Information and Event Management (SIEM):
SIEM systems collect and aggregate log data generated throughout the organization’s IT infrastructure, from host systems and applications to network and security devices such as firewalls and antivirus filters. SIEM tools provide real-time analysis of security alerts generated by applications and network hardware. Examples include Splunk, LogRhythm, IBM QRadar, and ArcSight.
2. Intrusion Detection System/Intrusion Prevention System (IDS/IPS):
IDS/IPS tools monitor network traffic to identify suspicious activities that could indicate a network or system attack from someone attempting to break into or compromise a system. Examples include Snort, Suricata, and Cisco FirePOWER.
3. Endpoint Detection and Response (EDR):
EDR tools monitor and collect data from endpoints, looking for suspicious activity. These tools can help automate responses to detected issues. Examples include Crowdstrike Falcon, Microsoft Defender for Endpoint, and SentinelOne.
4. Threat Intelligence Platforms:
These tools help organizations understand and respond to the most common threats they face by pulling in information about threat trends and attack techniques from a variety of sources. Examples include Recorded Future, ThreatConnect, and Anomali.
5. Security Orchestration, Automation, and Response (SOAR):
SOAR tools help SOC teams handle alerts more efficiently and effectively by integrating different security tools and automating responses to low-level threats. Examples include Palo Alto XSOAR (formerly Demisto), IBM Resilient, and Splunk Phantom.
6. Vulnerability Management Software:
Vulnerability management tools help identify and remediate weaknesses that could be exploited by attackers. Examples include Qualys, Tenable Nessus, and Rapid7 InsightVM.
7. User and Entity Behavior Analytics (UEBA):
UEBA systems use machine learning, algorithms, and statistical analysis to detect abnormal behavior that might indicate a threat. Examples include Exabeam, Rapid7 InsightIDR, and Splunk User Behavior Analytics.
8. Digital Forensics and Incident Response (DFIR) Tools:
These tools are used after a security incident has occurred to understand what happened, how it happened, and what impact it had. They’re also used to gather evidence in a form that’s suitable for use in court if necessary. Examples include EnCase, FTK, and Autopsy.
9. Network Traffic Analysis (NTA) Tools:
These tools continuously analyze raw traffic and/or flow records to build models based on the identification and behavior of devices across your infrastructure to detect suspicious activity. Examples include Darktrace, Cisco Stealthwatch, and ExtraHop.
Remember that the selection of tools will vary depending on the specific needs and context of the organization. The best practice is to have a balanced mix of these tools that work together to provide comprehensive coverage of the organization’s infrastructure.
Hardware Costs
Your SOC will need adequate hardware to run all the necessary software effectively. This includes servers for hosting your SIEM and other tools, network devices for capturing traffic, and workstations for your analysts. Costs for hardware will again vary, but expect to budget between $10,000 to $50,000 for a small business and upwards of $100,000 for medium to large businesses.
An on-premise SOC requires substantial hardware infrastructure, which can include:
- Servers: SOC needs a robust server infrastructure to run security software like SIEM (Security Information and Event Management), IDS/IPS (Intrusion Detection Systems/Intrusion Prevention Systems), vulnerability scanning tools, etc. These servers should be capable of processing and storing large amounts of data.
- Firewalls and Other Security Devices: SOC operations need advanced firewalls, IDS/IPS devices, and other security appliances to detect and prevent threats.
- Network Devices: This includes routers, switches, and other devices to support the data traffic.
- Workstations: Security analysts need high-performance computers to run security software, analyze data, and respond to incidents.
- Storage Devices: A SOC requires significant data storage capabilities, both for immediate analysis and for storing historical data for future analysis or compliance purposes.
- Backup Power Supplies and Generators: Since a SOC needs to operate 24/7, it’s critical to have backup power supplies and generators to ensure operations continue even during power outages.
MDR / XDR as a SOC alternative
Managed Detection and Response (MDR) or Extended Detection and Response (XDR) services are increasingly popular alternatives to building and operating an in-house Security Operations Center (SOC). Let’s compare and contrast the two options:
1. Cost:
MDR/XDR: These services are typically subscription-based, so they can be more predictable in terms of costs. They also do not require large upfront investments in hardware, software, and personnel.
In-house SOC: Building your own SOC can be expensive. You’ll need to invest in infrastructure, software, and, most importantly, skilled staff.
2. Staffing and Expertise:
MDR/XDR: These services provide access to teams of security experts who have wide-ranging experience in dealing with various threats. This can be especially beneficial for organizations that are unable to attract or retain such talent internally.
In-house SOC: Running your own SOC requires hiring and retaining a team of cybersecurity professionals. Given the shortage of skilled cybersecurity personnel, this can be challenging and expensive.
3. Availability:
MDR/XDR: MDR and XDR service providers typically offer 24/7 coverage, which can be important for quickly responding to security incidents.
In-house SOC: Providing 24/7 coverage with an in-house team can be difficult and costly, particularly for smaller organizations.
4. Customization:
MDR/XDR: These services might not offer the same level of customization or flexibility as an in-house SOC. You may have to adapt to the tools, procedures, and processes used by the service provider.
In-house SOC: With your own SOC, you have complete control over the tools and processes used and can tailor them to meet your specific needs.
5. Focus:
MDR/XDR: Outsourcing to an MDR/XDR allows your internal IT team to focus on core business functions instead of managing security incidents.
In-house SOC: Operating your own SOC means that security is handled in-house, potentially providing more control but requiring a significant commitment of resources.
6. Scalability:
MDR/XDR: These services can scale up or down more easily with your needs, as they’re typically based on a subscription model.
In-house SOC: Scaling your own SOC can be more complex and time-consuming, as it might require hiring additional staff, purchasing more hardware, etc.
7. Data Control and Privacy:
MDR/XDR: When using these services, you must entrust your security data to a third party, which could pose potential privacy and data sovereignty issues. Make sure that the service provider can attest to data governance.
In-house SOC: With an in-house SOC, you maintain control over all of your data, which could be important for meeting certain regulatory or business requirements.
Ultimately, the choice between using MDR/XDR services and building your own SOC depends on various factors, including your organization’s size, industry, risk profile, regulatory environment, budget, and IT strategy. Some organizations may even opt for a hybrid approach, where certain functions are outsourced while others are handled in-house.
Thanks for reading this far.
My aim with this campaign is to provide readers with valuable content, insights, and inspiration that can help in their personal and professional lives. Whether you’re looking to improve your productivity, enhance your creative strategies, or simply stay up-to-date with the latest news and ideas in cybersecurity, I’ve got something for you.
But this campaign isn’t just about sharing our knowledge and expertise with you. It’s also about building a community of like-minded IT and security focused individuals who are passionate about learning, growing, and collaborating. By subscribing to the blog and reading every day, you’ll have the opportunity to engage with other readers, share your own insights and experiences, and connect with people in the industry.
So why should you read every day and subscribe? Well, for starters, you’ll be getting access to some great content that you won’t find anywhere else. From practical tips and strategies to thought-provoking insights and analysis, the blog has something for everyone that wants to get current and topical cybersecurity information. Plus, by subscribing, you’ll never miss a post, so you can stay on top of the latest trends and ideas in the field.
But perhaps the biggest reason to join the 30-in-30 campaign is that it’s a chance to be part of something bigger than yourself. By engaging with the community, sharing your thoughts and ideas, and learning from others, you’ll be able to grow both personally and professionally. So what are you waiting for? Subscribe, and for the next 30 days and beyond, let’s learn, grow, and achieve our goals together!
Discover more from Designing Risk in IT Infrastructure
Subscribe to get the latest posts sent to your email.
One thought on “Building a Security Operations Center: A Comprehensive Guide for Businesses of all Sizes”
Comments are closed.