Welcome to the 30-in-30 blog campaign! I’m excited to launch this initiative, which involves publishing a brand new blog post every single day for the next 30 days. I will not mince words about this. It is hard to keep it up, stay engaging, relevant and interactive. More about this campaign is at the end of this article.
The Dark Web, a part of the internet hidden from conventional search engines, has gained a notorious reputation due to its association with illegal activities. However, it is also home to legitimate and valuable content. If you’re curious about exploring the Dark Web, it’s essential to understand the potential risks and take necessary precautions to ensure your safety and privacy. In this step-by-step guide, we will walk you through accessing the Dark Web safely.
Disclaimer: Accessing the Dark Web can expose you to illegal content, scams, malware, and other security risks. Proceed with caution and adhere to the laws and regulations of your jurisdiction.
Step 1: Understand the Basics Before delving into the Dark Web.
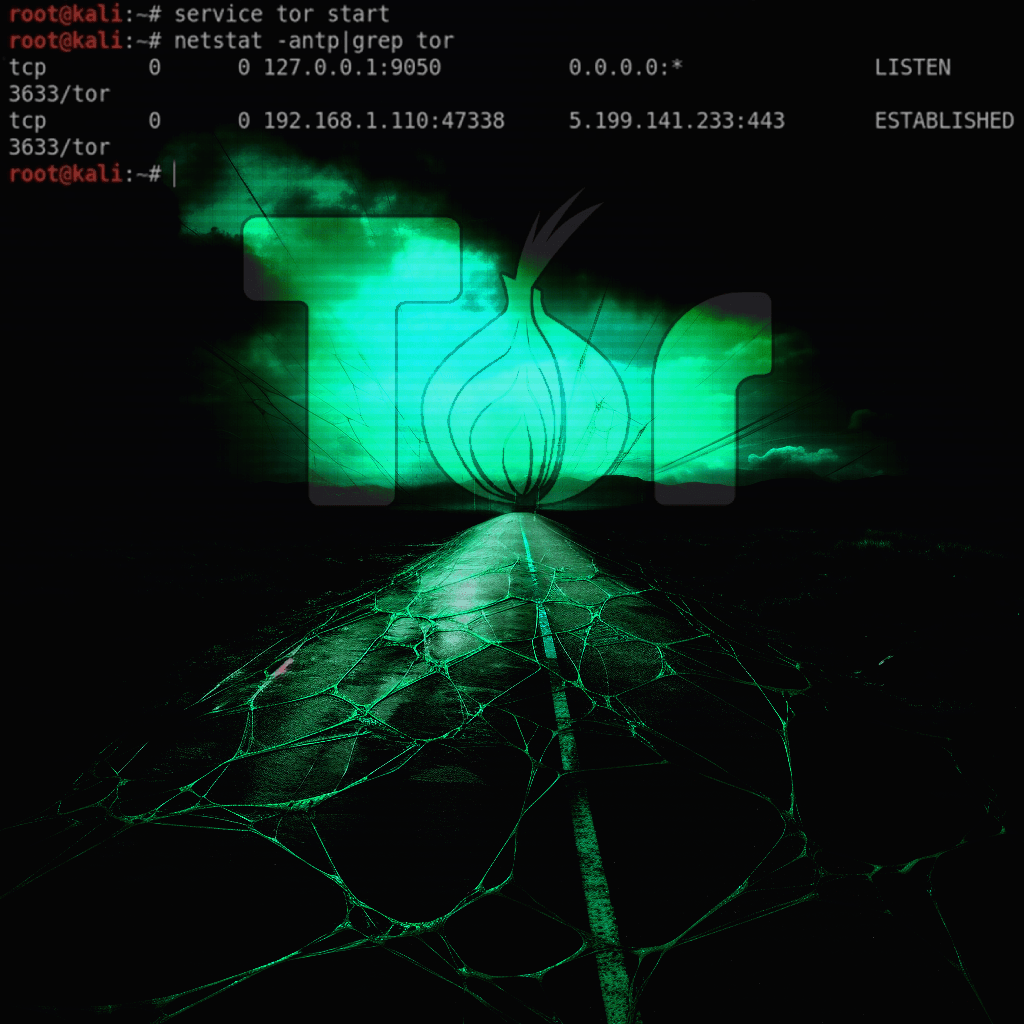
It’s crucial to understand its structure and terminology. The Dark Web refers to the encrypted network that exists within the Deep Web, which includes websites not indexed by search engines. The most common way to access the Dark Web is through a specialized browser called Tor (The Onion Router).
Step 2: Install Tor Browser To access the Dark Web.
You need to download and install the Tor Browser. It is based on Mozilla Firefox and routes your internet traffic through multiple volunteer-operated servers to anonymize your online activities. Visit the official Tor Project website (https://www.torproject.org) and download the latest version of the Tor Browser compatible with your operating system.
Step 3: Verify the Downloaded Tor Browser.
To ensure the authenticity and integrity of the Tor Browser, verify its signature. Instructions for verifying the signature can be found on the Tor Project website. This step helps prevent tampering and ensures you are using the official Tor Browser version. For a more secure experience, it is highly recommended that you run Tor from a privacy dedicated OS. Tails is a good option for that, and it can boot directly from a USB drive. https://tails.boum.org/
Step 4: Launch the Tor Browser.
Once the Tor Browser is installed, launch it like any other application. The Tor Browser may take slightly longer to connect to the internet due to the encryption and routing processes.
Step 5: Configure Your Tor Browser Settings.
To enhance your privacy and security while accessing the Dark Web, configure your Tor Browser settings. Click on the Tor Browser menu (three horizontal lines) and select “Preferences.” Here are some essential settings to consider:
- Security Level: Set it to “Safest” to enable the most robust security features.
- Disable JavaScript: Go to “Privacy & Security” and uncheck “Enable JavaScript.” This mitigates potential vulnerabilities.
Step 6: Connect to the Tor Network.
After configuring the settings, click on the “Connect” button in the Tor Browser to connect to the Tor network. This step establishes the necessary encrypted connections to ensure your anonymity.
Step 7: Understand Onion Links Websites on the Dark Web.
Use onion links (URLs with the “.onion” domain) instead of conventional domain names. Onion links are designed to be more resistant to censorship and provide better anonymity. Be cautious when accessing onion links, as they can lead to illicit content.
Step 8: Find Dark Web Directories and Search Engines.
To navigate the Dark Web effectively, you can utilize Dark Web directories and search engines. These platforms index and categorize websites available on the Dark Web, making it easier to find legitimate content. Examples include Torch (http://xmh57jrzrnw6insl.onion/) and Ahmia (http://msydqstlz2kzerdg.onion/).
Step 9: Be Cautious and Use Common Sense While accessing the Dark Web.
Exercise caution and follow these best practices:
- Never share personal information or engage in transactions involving sensitive data.
- Avoid downloading files from unknown sources, as they may contain malware.
- Stay away from illegal activities, and respect the law at all times.
- Keep your operating system, antivirus, and Tor Browser up to date
For a more in depth step by step walk-through, I recommend watching TCM Security Academy’s (The Cyber Mentor) video on it. Its a good one.
Thanks for reading this far.
My aim with this campaign is to provide readers with valuable content, insights, and inspiration that can help in their personal and professional lives. Whether you’re looking to improve your productivity, enhance your creative strategies, or simply stay up-to-date with the latest news and ideas in cybersecurity, I’ve got something for you.
But this campaign isn’t just about sharing our knowledge and expertise with you. It’s also about building a community of like-minded IT and security focused individuals who are passionate about learning, growing, and collaborating. By subscribing to the blog and reading every day, you’ll have the opportunity to engage with other readers, share your own insights and experiences, and connect with people in the industry.
So why should you read every day and subscribe? Well, for starters, you’ll be getting access to some great content that you won’t find anywhere else. From practical tips and strategies to thought-provoking insights and analysis, the blog has something for everyone that wants to get current and topical cybersecurity information. Plus, by subscribing, you’ll never miss a post, so you can stay on top of the latest trends and ideas in the field.
But perhaps the biggest reason to join the 30-in-30 campaign is that it’s a chance to be part of something bigger than yourself. By engaging with the community, sharing your thoughts and ideas, and learning from others, you’ll be able to grow both personally and professionally. So what are you waiting for? Subscribe, and for the next 30 days and beyond, let’s learn, grow, and achieve our goals together!
Discover more from Designing Risk in IT Infrastructure
Subscribe to get the latest posts sent to your email.
One thought on “30in30 – Post 15 – How to Access the Dark Web Safely”
Comments are closed.