Welcome to the 30-in-30 blog campaign! I’m excited to launch this initiative, which involves publishing a brand new blog post every single day for the next 30 days. I will not mince words about this. It is hard to keep it up, stay engaging, relevant and interactive. More about this campaign is at the end of this article.
The Canadian Security Establishment (CSE) is a signals intelligence agency that serves as the technical authority for cyber security and information assurance in Canada. It includes the Canadian Centre for Cyber Security, which acts as the federal government’s operational lead for cyber security.
The CSE’s mandate is outlined in the CSE Act and encompasses five main areas:
- foreign signals intelligence
- cyber security
- active cyber operations
- defensive cyber operations
- technical and operational assistance to federal partners
This report is vast and highlights many of the activities that CSE has been doing in 2021-2022. I have only selected a few to highlight and discuss. Read the full report to get more detailed information. These are key sections from the report I have pulled:
- Cybersecurity support for Operation UNIFIER in Ukraine
- Attribution of large scale nation-state cyber attacks
- Active and Defensive foreign cyber operations
- Realtime engagement in Incident Response activities
- Threat Intelligence for critical infrastructure
- Malware analysis platform
- Threat Intelligence Feeds
- Threat intelligence for the public via DNS (Canadian Shield)
- Incident reporting portal
- Public cybersecurity advisories
- Training resources for SMB and Broader Public Sector
- Geekweek / Geekpeek (CSE Hackathon)
- New CSE created cybersecurity tools
There is a lot of interesting stuff in this report, and I’ll have to dig deeper into some individual aspects in future posts.
Russia’s invasion of Ukraine
In the weeks leading up to the invasion, the Cyber Centre issued two public advisories warning Canadian critical infrastructure organizations to bolster their defences against known Russian-backed cyber threat activity.
These advisories were informed by CSE SIGINT and Cyber Centre operational knowledge as well as Russia’s track record of using its cyber capabilities irresponsibly, such as:
- the SolarWinds cyber compromise
- activity aimed at COVID-19 vaccine research
- activity aimed at Georgia’s democratic process
- the NotPetya malware attacks on government and critical infrastructure targets around the world
Before, and throughout the invasion, the Cyber Centre continued to track cyber threat activity in Canada and around the world and to share that information with Canadian critical infrastructure partners. That threat feed includes:
- indicators of compromise (digital details about malicious activity)
- threat mitigation advice
- confidential alerts about:
- new forms of malware
- tactics being used to target victims
CSE continued to provide technical and operational assistance to Operation UNIFIER, the Canadian Armed Forces mission in support of Ukraine. This included intelligence sharing and cyber security support.
Attributions
CSE works with Global Affairs Canada and other federal and international partners to call out irresponsible behaviour in cyber space. CSE contributes to these attributions using both intelligence analysis and cyber security expertise.
In April 2021, Canada joined our allies in attributing the SolarWinds cyber compromise to a Russian state-sponsored actor. The threat activity compromised thousands of networks around the world, by installing malware through program updates. The threat actor then targeted a subset of those victims for cyber-espionage purposes.
In July 2021, Canada joined our allies in identifying People’s Republic of China (PRC) state-backed actors as responsible for the “unprecedented and indiscriminate” exploitation of Microsoft exchange servers. An estimated 400,000 servers were affected worldwide and used to steal intellectual property and vast quantities of personal information.
As mentioned above, in January and February 2022, the Cyber Centre joined our US and UK allies to warn and remind Canadian organizations about known Russian-backed cyber threats to critical infrastructure.
Foreign cyber operations
Foreign cyber operations (FCO) are the newest part of CSE’s mandate, dating back to the CSE Act in 2019. These authorities enable Canada to take action in cyberspace against foreign adversaries in matters relating to Canada’s international affairs, defence or security.
Subdivided into defensive cyber operations (DCO) and active cyber operations (ACO), these authorities give Canada the option of acting on what CSE learns through our SIGINT and cyber security missions.

Assisting the Canadian Armed Forces
CSE has also used its active cyber operations capabilities to assist the Canadian Armed Forces in support of their mission.
Incident management
“Cyber Incident: Any unauthorized attempt, whether successful or not, to gain access to, modify, destroy, delete, or render unavailable any computer network or system resource.”Canadian Centre for Cyber Security,Glossary
It is the nature of cyber security that even with the best defences, cyber incidents do occur.
The Cyber Centre offers 24/7 support to contain the threat and mitigate the damage when cyber incidents affect federal institutions or systems of importance to the Government of Canada.
This fiscal year, the Cyber Centre opened 2,023 cyber security incident cases. That’s an average of 5.5 per day. Of those cases, 1,154 were federal institutions, and 869 were critical infrastructure.
The types of incidents included:
- reconnaissance activity by sophisticated threat actors
- phishing incidents (emails containing malware)
- unauthorized access to corporate IT environments
- imminent ransomware attacks
- zero-day exploits (exploitation of critical vulnerabilities in unpatched software)
Depending on the nature and severity of the case, the incident management team offers:
- victim notifications
- tailored advice and guidance
- recovery assistance
- analysis reports
- digital forensics
We offer these services day in day out. This year, the Cyber Centre also provided incident response coordination and standby support for major planned events including:
- the 2021 Canadian federal election
- the 2021 Canadian census
- the COVID-19 vaccine rollout

Cyber security: critical infrastructure
“In 2021, the Cyber Centre was aware of 304 ransomware incidents against Canadian victims, over half of them in critical infrastructure. But we know cyber incidents are significantly underreported, and the true number of victims is much higher.”Sami Khoury,Head of the Canadian Centre for Cyber Security
CSE has a mandate to help improve the cyber resilience of Canada’s critical infrastructure (CI). This is a top priority for the Cyber Centre, and much of our focus this year has been about deepening and expanding our CI partnerships.
CI means the essential services we can’t do without, like healthcare, energy, finance, and communications. It is a lucrative target for ransomware gangs.
CI also faces threats from state-sponsored cyber actors, who may target CI assets as a form of geopolitical leverage. In early 2022, the Cyber Centre issued two threat bulletins alerting critical infrastructure about known Russian-backed cyber threat activity.
If CSE learns of a cyber threat, either through foreign signals intelligence, or while maintaining the government’s cyber defences, we share that information with as many trusted critical infrastructure providers as possible.
Case study: support to Newfoundland and Labrador
In the fall of 2021, the healthcare system of Newfoundland and Labrador was impacted by a serious cyber incident. Thousands of medical procedures had to be cancelled and thousands of patient files were breached.Footnote3
The Cyber Centre worked closely with the province and our federal partners to coordinate the IT portion of the response. This included sending a team to provide hands-on cyber security support. Over the course of several months the Cyber Centre provided:
- on-site support (3 weeks)
- remote assistance
- tailored advice and guidance
- digital forensics
- mitigation (recovery) assistance
- information sharing
- analytical reports
- advice on rebuilding infrastructure
New funding in Budget 2022 will enable the Cyber Centre to offer more help of this kind in the event of high-impact cyber incidents on Canada’s critical infrastructure.
Cyber security services
The Cyber Centre encourages eligible CI partners to sign up for our free, confidential cyber security services. These include, but are not limited to:
- incident management
- threat intelligence
- alerts about cyber threats (plus mitigation steps)
- weekly incident summaries
- regular cyber threat briefings
- notifications about malicious activity on their IP space
- access to our malware analysis platform
- access to our automated threat intelligence feed
- sector-specific community outreach and engagement
- a dedicated Cyber Centre point of contact
Cyber Centre services do not replace commercial solutions, but they help CI providers tailor their cyber defences based on reliable information and expert advice. Partners can choose the level of service that best meets their needs, or engage with the Cyber Centre for advice and guidance as and when they need it.
Malware analysis platform
Assemblyline is the Cyber Centre’s malware detection and analysis platform. Analysts submit suspicious files, and Assemblyline checks them against the Cyber Centre’s unique database of cyber threats. If the sample is malicious, Assemblyline provides details about the malware strain to help inform the response.
At first, Assemblyline could only be used within CSE on our classified network, where we use it to help defend the Government of Canada from cyber threats. But over the years, we have found ways to share it externally, so that other cyber defenders can benefit from it.
CSE first released the software for Assemblyline in 2017, allowing others to build their own platforms using our code. Over 3,000 organizations downloaded these do-it-yourself versions of Assemblyline. Since then, the Cyber Centre has re-written Assemblyline from the ground up.
The latest version, Assemblyline 4, is cloud-compatible, and it has a new database, a new user interface and new malware detection capabilities. We released it open source in January 2020 and completed its implementation on our classified network in February 2022.
In the interim, we created two new Assemblyline platforms that our external partners can use for free: one for government clients and one for critical infrastructure partners. This was made possible by major investments in our IT infrastructure during the pandemic. With that groundwork done, we can support more services at the unclassified level and Protected B (a mid-level security classification).
Now, instead of emailing samples to the Cyber Centre and waiting days for a manual analysis, external partners simply log in, submit their suspicious files for analysis and get a result within minutes.
Automated threat intelligence feed
Aventail is the Cyber Centre’s automated threat intelligence sharing service. It provides critical infrastructure partners with relevant, verified information about Indicators of Compromise (IoCs) at machine speed. IoCs are details about cyber threats, such as:
- domains and URLs (elements of web addresses)
- IP addresses (numeric codes that identify devices on the Internet)
Cyber defenders use IoCs to prevent and mitigate malicious activity on their networks. This year, Aventail shared 46,965 unique IoCs. That’s an average of 129 a day.
CSE has shared its threat feed with Government of Canada departments and our Five Eyes partners since 2017. In March 2020, the Cyber Centre launched Aventail so we could share it directly with CI partners. This year our client base for Aventail has grown from 80 to 122 CI partners.
The Cyber Centre also shares Aventail with CIRA (the Canadian Internet Registration Authority) to enhance their threat-blocking service, Canadian Shield.
Aventail is part of the Cyber Centre’s strategy to create tools and build partnerships that raise the bar for cyber security in Canada.
New cyber incident reporting portal
In May 2021, the Cyber Centre launched a new feature on our website, to make it easier to report a cyber incident.
Cyber incident reporting helps the Cyber Centre keep Canada and Canadians safe online by giving us a more accurate picture of the cyber security landscape. We use that information to inform our advice, guidance and services.
The portal allows government departments, critical infrastructure providers and IT practitioners to report incidents directly to the Cyber Centre. Depending on the circumstances we can offer them advice and guidance.
The portal directs Canadian individuals and small or medium organizations to the right partner for different incident types. For instance, the RCMP or local police handle cybercrime investigations, while the Spam Reporting Centre gathers complaints about unsolicited emails and texts.
Sharing our threat feed to benefit Canadians
The Cyber Centre works with trusted partners to improve cyber security for Canadians in their daily lives. Our partnership with CIRA is a prime example.
CIRA Canadian Shield is a free service that protects Canadians’ privacy on their home networks and personal devices. It also has a threat-blocking option that prevents users from inadvertently connecting to known malicious sites. The Cyber Centre shares its automated threat intelligence feed with CIRA, so that any threats we have identified will also be blocked by Canadian Shield.
As of March 31, 2022, more than 177,000 users have signed up for Canadian Shield’s threat-blocking services, which recorded more than 88 million blocks this year.
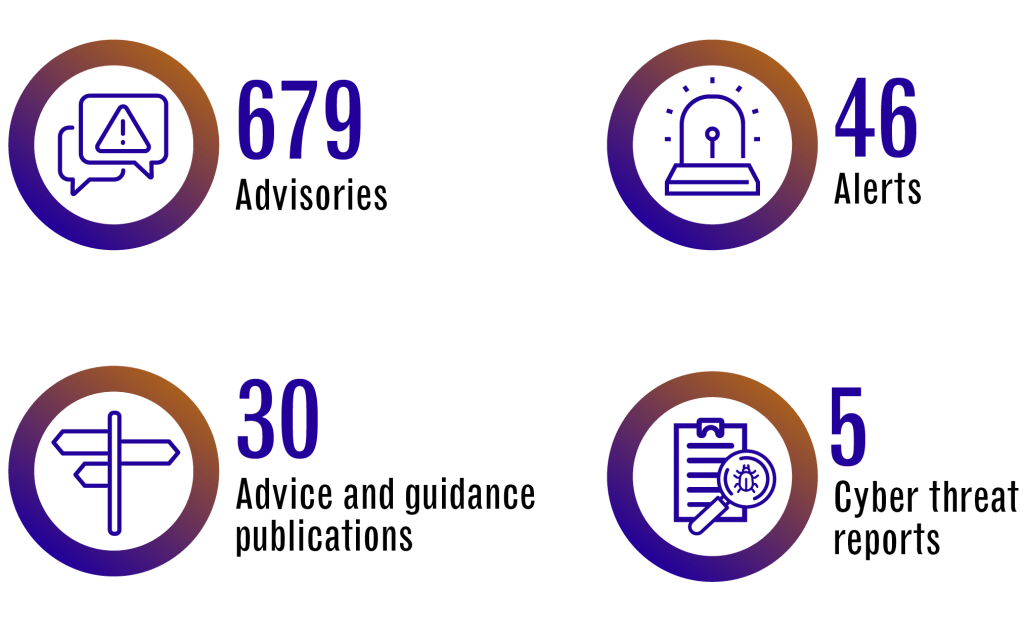
Alerts and advisories
The Cyber Centre issues alerts and advisories for IT professionals. These outline recommended actions on specific cyber threats ranging from routine software updates (advisories) to critical vulnerabilities (alerts).
For example, in December 2021, the Cyber Centre published 1 joint advisory and 8 alerts about the Apache Log4j vulnerability.
These alerts and advisories are posted on our website and social media channels. We also email alerts directly to Cyber Centre clients. As of March 31, 2022, 2701 contacts from 832 organizations subscribed to this service
The Learning Hub
The Learning Hub is based at the Cyber Centre and provides training to improve the cyber security of Canada’s government and critical infrastructure organizations.
Training for small and medium organizations
The Learning Hub worked with Innovation, Science and Economic Development Canada (ISED) to develop free cyber security training for small and medium organizations. ISED’s CyberSecure Canada eLearning series consists of 14 self-paced modules for learners with minimal technical knowledge. The modules can be taken as part of ISED’s CyberSecure certification process, or simply to improve cyber awareness and resilience.
Training for public servants
This year, the Learning Hub renewed their collaboration with the Canada School of Public Service (CSPS) to provide a standardized cyber security curriculum for all federal public servants. For example, the Learning Hub and CSPS co-developed an e-learning course to introduce public servants from non-technical backgrounds to the basics of cloud computing. This is a priority topic for the public service as departments continue to migrate their IT infrastructure to the cloud.
GeekWeek
GeekWeek is the Cyber Centre’s annual cyber security workshop at the unclassified level. It brings together participants from government, industry and academia. Every year GeekWeek participants work on more than 30 different projects to solve hard cyber security problems.
Past GeekWeek events have taken place in the fall, but future events will be held in the spring. As a result of that switch, there was no GeekWeek this year. However, the work begun at GeekWeek events continues year-round as CSE employees find ways to take ideas from proof-of-concept to implementation.
For example, Chameleon is a configurable software that can be used offline as a network simulator, or online as a network honeypot. A honeypot is a decoy target used to attract cyber threat activity in order to study it and defend against it. Chameleon was developed over the course of 4 GeekWeek events by over 50 participants from different organizations. It can currently emulate more than 154 cyber security vulnerabilities.
In March 2022, the Cyber Centre finalized the code for Chameleon and released it back to the GeekWeek community for a Canadian wide impact.
GeekWeek innovations have contributed to many other Cyber Centre tools including several mentioned in this report:
- Assemblyline
- Aventail
- Tracker
- the sharing hub to help protect Canadians against phishing
GeekPeek
New this year, GeekPeek is an unclassified hackathon for Canadian graduate and undergraduate students in fields related to cyber security.
In December 2021, the Cyber Centre welcomed 26 students from 7 universities across Canada for the first edition of GeekPeek. For 5 days, they worked with Cyber Centre professionals on problems related to:
- machine learning
- network traffic analysis
- cyber threat hunting
- malware reversing
From January to March 2022 the Cyber Centre ran a “capstone edition” of GeekPeek in collaboration with Queen’s University. Cyber Centre employees mentored 25 students working on their capstone projects (applied research in the final year of study). Cyber Centre judges evaluated the projects at the end of March, with the best presentations shown at GeekWeek 2022.
Developing and improving cyber security tools
The Cyber Centre designs and shares tools so that government departments can assess their own cyber security more efficiently. Below are some examples of technologies we improved upon this year.
Observation Deck

Observation Deck is a web application the Cyber Centre offers to government departments in our host-based sensor program. The platform lets users view data from the sensors on their department’s IT infrastructure so they can make informed decisions about their cyber security.
More than 40 departments have adopted Observation Deck since its launch in 2020. In November 2021, the Cyber Centre rolled out a new version based on user feedback. The redesign has better search functionality and new reporting views. It also lets users generate and export datasets, including custom charts.
Over the past year, the Cyber Centre has used Observation Deck to help our partners respond to numerous cyber security events, including Log4j and #PrintNightmare.
ASTRA
( Analytical Software for Threat Assessment)
ASTRA is a threat risk assessment tool created by the Cyber Centre to help Government of Canada departments evaluate the level of cyber risk to their IT assets. For example, it could be used at the beginning of a project to evaluate the cyber security of different network architectures.
The interface walks users step by step through the risk assessment process, similar to the way income tax software helps you fill in a tax return.
ASTRA allows users to:
- identify risks of concern
- recommend solutions
- track risk levels over the course of a project
Prior to this year, ASTRA existed as a standalone platform hosted by the Cyber Centre. In March 2022, the Cyber Centre released an enterprise version of ASTRA which client departments could download onto their own networks. This allows whole teams to work with the same information and makes the whole process more convenient. By the end of the fiscal year, 53 departments had downloaded ASTRA to help them assess their cyber risks.
Tracker

Tracker is an automated self-assessment tool for Government of Canada departments and agencies. The interactive platform allows users to check the security configuration of their public facing websites and email services. This helps to:
- prevent cyber criminals from spoofing government email domains
- secure the online services Canadians rely on
- protect the reputation of the Government of Canada
Tracker was co-developed by the Cyber Centre and the Treasury Board of Canada Secretariat (TBS) based on TBS’s HTTPS-Everywhere tool. The updated version makes it easier for departments to check their compliance with both TBS policy and Cyber Centre guidance. It launched in October 2021 and is being used by close to 100 Government of Canada organizations.
Thanks for reading this far.
Now my aim with this campaign is to provide readers with valuable content, insights, and inspiration that can help in their personal and professional lives. Whether you’re looking to improve your productivity, enhance your creative strategies, or simply stay up-to-date with the latest news and ideas in cybersecurity, I’ve got something for you.
But this campaign isn’t just about sharing our knowledge and expertise with you. It’s also about building a community of like-minded IT and security focused individuals who are passionate about learning, growing, and collaborating. By subscribing to the blog and reading every day, you’ll have the opportunity to engage with other readers, share your own insights and experiences, and connect with people in the industry.
So why should you read every day and subscribe? Well, for starters, you’ll be getting access to some great content that you won’t find anywhere else. From practical tips and strategies to thought-provoking insights and analysis, the blog has something for everyone that wants to get current and topical cybersecurity information. Plus, by subscribing, you’ll never miss a post, so you can stay on top of the latest trends and ideas in the field.
But perhaps the biggest reason to join the 30-in-30 campaign is that it’s a chance to be part of something bigger than yourself. By engaging with the community, sharing your thoughts and ideas, and learning from others, you’ll be able to grow both personally and professionally. So what are you waiting for? Subscribe, and for the next 30 days and beyond, let’s learn, grow, and achieve our goals together!
Discover more from Designing Risk in IT Infrastructure
Subscribe to get the latest posts sent to your email.
One thought on “30in30 – Post 9 – Review of key elements in the Communications Security Establishment (CSE) Annual Report 2021-2022”
Comments are closed.