
June 2022 was when the first reading of Bill C-26 was done in parliament. The full title of the Bill is:
“Act Respecting Cyber Security, amending the Telecommunications Act and making consequential amendments to other Acts”.
Bill C-26 can also be called “ARCS” for short.
If you want to dig into the actual wording on the bill, have a gander at it here.
There are a few things this bill does. The first is to provide an amendment to the Telecommunications Act. The second is to enact the CCSPA (Critical Cyber Systems Protection Act).
In this post I will discuss how the CCSPA will affect the energy sector
How the CCSPA will affect Interprovincial or International Pipeline and Power Line Systems, and Nuclear Energy Systems.
| Scope | Interprovincial or International Pipeline and Power Line Systems, and Nuclear Energy Systems have been identified in the legislation as systems that are vital to national security and/or public safety. The CCSPA authorizes the Federal Cabinet to designate a class of operators in respect of these systems who must comply with the requirements of the legislation. A class of operators could include interprovincial pipelines that cross provincial borders and international pipelines that cross the Canada-U.S. border. |
| Responsible Regulator | The Canadian Energy Regulator (CER) is the regulator charged with administering the CCSPA in respect of interprovincial or international pipeline and power line systems. The Canadian Nuclear Safety Commission (CNSC) is the regulator charged with administering the CCSPA in respect of nuclear energy systems. The legislation also imposes a reporting obligation to the Communications Security Establishment (CSE), Canada’s national cryptologic agency. |
| Cybersecurity Programs | Designated operators will be required to establish a cyber security program (CSP) within 90 days of being designated under the CCSPA. The CSP must:include reasonable steps to identify and manage organizational cybersecurity risks; include reasonable steps to protect critical cyber systems from being compromised, detect cybersecurity incidents and minimize related impacts; be reviewed and updated annually, or more frequently if specified by regulation; and be filed with CER/CNSC of Canada including notices of any updates to the CSP following periodic reviews. |
| Supply Chain Management | Designated operators must take reasonable steps to mitigate any identified cybersecurity risks associated with the designated operator’s supply chain or use of third-party products and services. These risk management measures must also be addressed in the operator’s CSP. |
| Change of Control Reporting | Designated operators are required to notify the CER or the CNSC, as applicable, of any material changes to ownership and/or control as well as to its supply chain or use of third-party products and services. |
| Cybersecurity Incident Reporting | Designated operators will be required to report a “cybersecurity incident” in a two-step process. A “cybersecurity incident” is any incident that interferes or may interfere with the continuity or security of a vital service or system, or the confidentiality, integrity or availability of the critical cyber system. First, designated operators must “immediately” report a cybersecurity incident to the CSE in a manner to be set out in the CCSPA’s regulations. Second, designated operators must notify the CER or the CNSC, as applicable, “immediately after reporting a cybersecurity incident” to the CSE. For nuclear energy operators, the obligations to report a cybersecurity incident complement their obligations under the General Nuclear Safety and Control Regulations (CNSCR) to report any theft or loss of prescribed information to the CNSC. |
| Recordkeeping | Designated operators must keep certain records, including copies of reported cybersecurity incidents and evidence of various security and related measures required under the CCSPA. These required records must be kept in Canada in accordance with additional guidance that may be established by the CER/CNSC or regulations. Nuclear energy companies will be familiar with the recordkeeping requirements under the CNSCR, and the obligations to notify the CNSC of any proposed disposal of records. However, the CCSPA obligations go above and beyond these established recordkeeping requirements. Federally regulated pipeline operators will also be familiar with the recordkeeping requirements under the Canadian Energy Regulator Onshore Pipeline Regulations (CEROPR). However, the CCSPA obligations supplement these obligations and add additional recordkeeping requirements. |
| Compliance with Directions | The CCSPA grants the Federal Cabinet broad authority to issue directions to designated operators ordering them to comply with any measure for the purpose of protecting a critical cyber system. The CER or the CNSC are also granted powers to order a designated operator to stop doing anything that is or is likely to be in contravention of the CCSPA or to take any measure that is necessary to ensure compliance or mitigate noncompliance with the CCSPA. |
| Disclosure Restrictions on Confidential Information | The CCSPA prohibits the disclosure of certain confidential information obtained under the CCSPA in respect of a designated operator’s critical cyber system. Disclosure of directions issued by the Federal Cabinet or the CER/CNSC under the CCSPA is also generally prohibited. |
| Inspections and Audits | The CER and the CNSC, as applicable, are granted broad audit and inspection powers under the CCSPA, which are not limited to the physical premises of the designated operator. The CER and the CNSC, as applicable, may also order a designated operator to conduct an internal audit of its practices, books and other records to determine compliance with the CCSPA. These broad inspection powers are in addition to those previously provided to the CER under the CEROPR and the CNSC under the Nuclear Safety and Control Act (NSCA). |
| Enforcement | Enforcement of the CCSPA includes administrative monetary penalties regime for noncompliance with the legislation. Of course, operators in the nuclear energy sector will be familiar with the administrative penalties regime under the Administrative Monetary Penalties Regulations (Canadian Nuclear Safety Commission) (AMPR CNSC) as will operators with federally regulated pipelines under the Administrative Monetary Penalties Regulations (National Energy Board) (AMPR NEB). Directors and officers of designated operators are party to any violations of the CCSPA if they direct, authorize, participate, assent to, or acquiesce in the commission of the violation. This is not dissimilar to the liability under the NSCA or the Canadian Energy Regulator Act. The CCSPA states that the purpose of a penalty is to promote compliance and not to punish. The CCSPA allows a designated operator or their directors and officers to raise a due diligence defence in a violation proceeding. The range of penalties are to be prescribed by regulation, but CCSPA authorizes a maximum penalty of C$15-million for designated operators and C$1-million for directors and officers. These are significantly higher than the penalties prescribed under the AMPR CNSC and the AMPR NEB. Noncompliance with certain provisions of CCSPA may alternatively be prosecuted as an offence punishable with criminal fines and/or imprisonment. The CCSPA also authorizes the CER and the CNSC, as applicable, to enter into a compliance agreements with a designated operator in respect of the operator’s obligations under the CCSPA. |
First let’s look at the scope. This legislation applies to:
- Interprovincial or International Pipeline
- Power Line Systems
- Nuclear Energy Systems
Interprovincial or International Pipelines
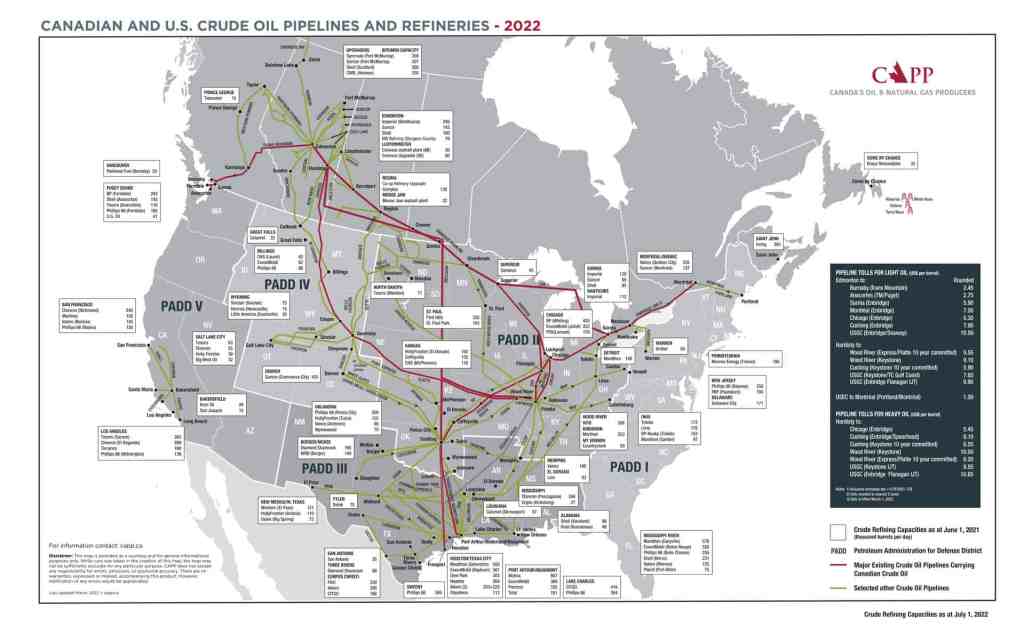
In Canada, Edmonton Alberta is the epicenter of the oil and gas industry. You can see that on the map below. Theres a reason the NHL team for that city is called the Oilers. There are also interprovincial / national pipelines that span the country. You can see company names associated with the refining locations, such as Suncor, Shell, Cenovus, Imperial, etc. There are more than 840,000 kilometres (km) of pipelines across Canada, and they are all regulated. The federal government regulates large transmission pipelines that cross provincial boundaries. The remaining pipelines are regulated provincially
There are number of different types of pipelines:
Gathering Pipelines
Gathering pipelines consist of about 250,000 km of small-diameter (4″ to 12″) pipelines that are used to move crude oil and natural gas within producing areas, from wells to oil batteries.
Feeder Pipelines
Feeder pipelines make up about 25,000 km of pipelines and are primarily in western Canada’s producing areas.
Transmission Pipelines
Transmission pipelines are large-diameter pipelines that move crude oil and natural gas within provinces and across provincial or international boundaries. Canada has about 117,000 km of transmission pipelines.
Distribution Pipelines
Distribution pipelines are operated by local distribution companies to deliver natural gas to final consumers in various industries, homes and businesses.There are about 450,000 km of distribution pipelines in Canada
Pipelines that cross provincial or international borders are regulated by the Canadian Energy Regulator (CER). Smaller pipelines within each province are under provincial regulation and not in the scope of Bill C-26.
Power Line Systems
The Canadian and US power grid is deeply inter-twined and managed by the North American Electric Reliability Corporation (NERC). This is divided into 5 area interconnects. Western, Eastern, Quebec, and Texas. Alaska is an affiliate, but has no interconnect with the other regions.
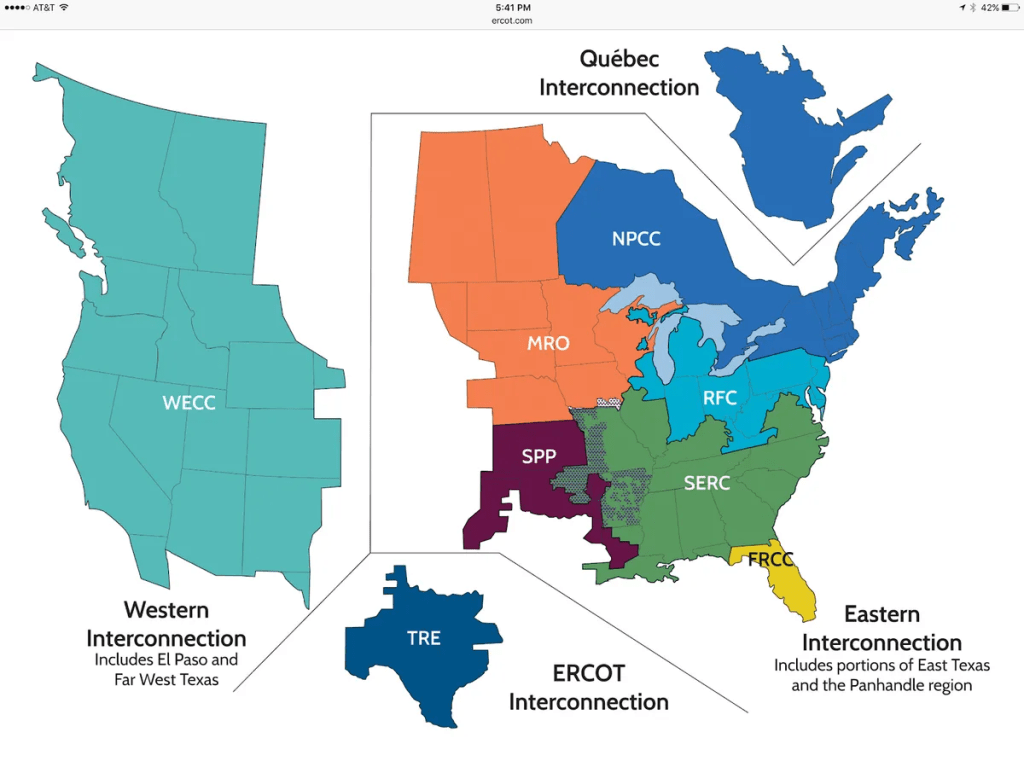
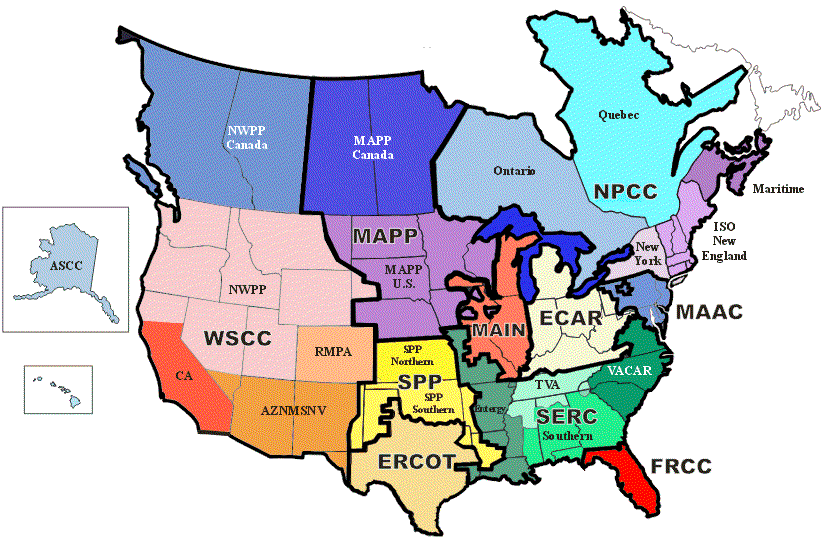
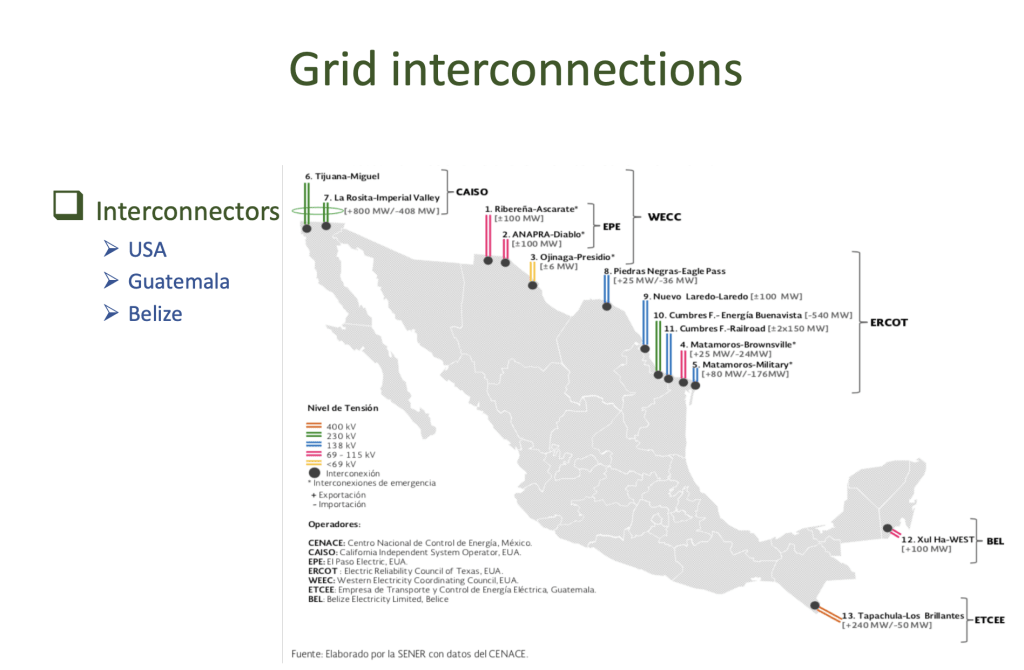
Mexico is independently operated and regulated by La Comisión Federal de Electricidad (CFE). However there are numerous connections with NERC and it is an energy exporter. This has been beneficial to areas that have deficiencies in their local production capabilities, or are impacted by external factors. California for example has had massive power issues with rolling blackouts during peak use periods. Texas also has some big problems that it needs to resolve. Both these regions can have some impact mitigated by the interconnections with the Mexican grid. There is a long term plan to unify the grid into a true North American grid with all three countries, but politics will make that a long term aspiration. Currently the Eastern and Western interconnects do not have large pipes between them, so that would be the first step.
Nuclear Energy Systems
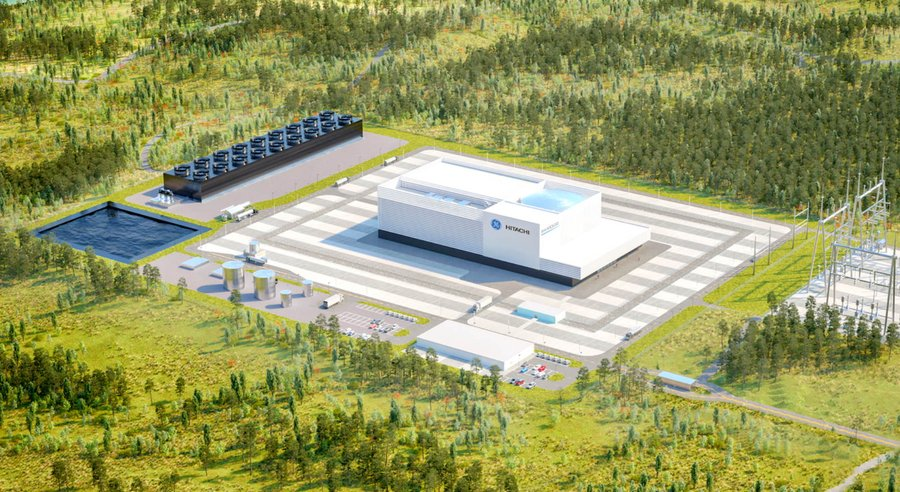
Nuclear power in Canada is provided by 19 commercial reactors with a net capacity of 13.5 gigawatt (GW). There are different size reactors that have a variety of purposes from power generation, to research and experimentation, to small site power systems not connected to the grid. The future of nuclear power is what is referred to as SMRs, or small modular reactors. The Canadian government just invested $1B to develop an SMR that can be grid connected. This would make nuclear energy systems fairly portable and distributable not only across Canada, but around the world.
Currently the reactor types that are the most commonly deployed in Canada are:
SLOWPOKE
Or the Safe LOW POwer (K)Critical Experiment. This was first designed in the 1960s and had a very low output (2kW). The second generation (SLOWPOKE-2) had an output of 20kW. These were sold to the Royal Military College of Canada, Polytechnique Montréal, and the University of the West Indies in Jamaica.
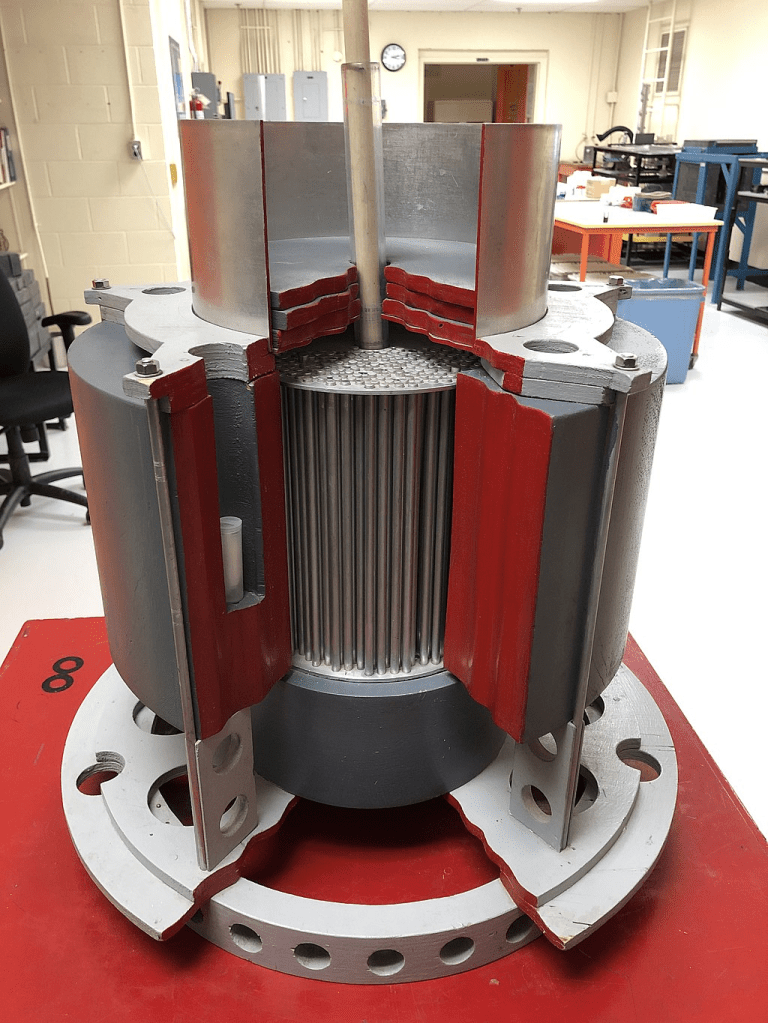
CANDU
The CANDU (Canada Deuterium Uranium) is a Canadian pressurized heavy-water reactor design (PHWR) used to generate electric power. The CANDU 6 produces 600 MWe. Ontario is the primary source for nuclear power generation in Canada.

BWRX-300
At the end of 2016 BWXT completed the acquisition of GE Hitachi Nuclear Energy Canada Inc. So some references still refer to GEH-C when discussing these reactors. he BWRX-300 is the 10th evolution of the BWR (boiling water reactor) technology Small modular reactors are nuclear facilities that are far smaller than traditional plants and this SMR would power about 300,000 homes. The first Darlington SMR is set to start producing energy in 2028.
The Canadian Energy Regulator (CER), Canadian Nuclear Safety Commission (CNSC), and NERC already have fairly robust security standards in place which designated operators must abide by. However, the CCSPA will expand on that and require the following:
1. Within 90 days of Bill C-26 being enacted, a Cybersecurity plan needs to be established.
- Within the CSP, it should include steps to identify and remediate cybersecurity risks. This should include a risk management practice that keeps a continual watch on threats, where the organization is vulnerable, the likelihood of breach and the impact thereof. There should also be a plan in place to increase the security posture over time. and to limit the attack surfaces.
- Annual reviews (at a minimum) of the CSP, with updates provided to CER/CNSC
2. Any changes to the ownership / control of the organization require CER or the CNSC, to be informed. This also applies to any changes within the supply chain as well.
3. The supply chain associated with the designated operators must meet certain standards to mitigate risks. The wording says: “reasonable steps to mitigate any identified cybersecurity risks associated with the designated operator’s supply chain or use of third-party products and services”. This is a broad statement and good be up for interpretation. I would imagine that the validation process for HW, software and 3rd party services to be used would have to meet stringent requirements.
4. Any cybersecurity incident will have to immediately be reported to the Communications Security Establishment (CSE), then directly after to CER or CNSC
5. All records of cybersecurity incidents, including logs and reports need to kept for a period of time defined by CER or CNSC, and they must remain in Canada.
6. If the government tells the designated operator to do something, like terminate services with a 3rd party or stop using a certain technology, they cannot disclose those details to anyone. In other words, follow the first rule of fight-club, or you will be in non-compliance.
7. If the government wants to audit an organization, they have carte blanche to do so. They can also just get organizations to do it themselves and provide detailed reports.
The legislation will improve the security posture of critical infrastructure in Canada, and something had to be done quickly and forcefully.
There is a full-scale global cyber war ongoing right now and it is not a matter of “if”, but “when” any given organization is breached. How well they are prepared will determine their continued viability as an entity. It’s like being told that a hurricane is coming and everybody needs to board up their homes. Whether or not it’s possible with the resources, time and skills at hand, remains to be seen for many.
However the onus is left on organizations to figure it out in very short order, and there is a massive shortage in staff with sufficient capabilities in the market. This is where an external company that focuses on cybersecurity can comes in and addresses all of the requirements of bill C-26 in a short period of time. I’ll write another article that describes in detail how they can do it, but in the meantime, have a look here.
Discover more from Designing Risk in IT Infrastructure
Subscribe to get the latest posts sent to your email.