Lennert Wouters, a security researcher at the Belgian University KU Leuven, has shown a working example of how to bypass the security of the Starlink User Terminal to gain access to other functions that are not normally available to users.
The presentation was done at BlackHat USA 2022. Here is a link to the writeup by Lennert.
Glitched on Earth by Humans: A Black-Box Security Evaluation of the SpaceX Starlink User Terminal
Here is the presentation slide deck.
Using a custom made modchip, he was able to implement a fault inject that bypassed the bootloader to install custom firmware. From there, he had root access to the terminal and could perform some functions such as beamforming and probing other parts of the Starlink network.
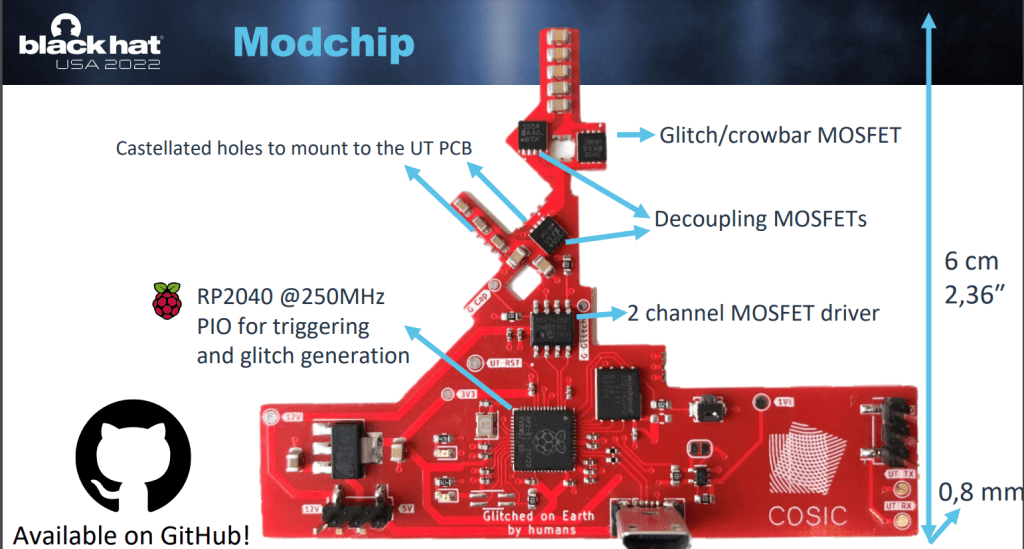
The hack is interesting as it is the first published hack on the Starlink User Terminal, but the process requires in-person access and there is not a lot that can be done with it yet. In the future, things like packet inspection, routing, logging, filtering, and URL redirection could be possible with the right tools.
Here is Starlinks response to the hack and an open invitation for more hacks in the future.
Discover more from Designing Risk in IT Infrastructure
Subscribe to get the latest posts sent to your email.